April 5, 2024
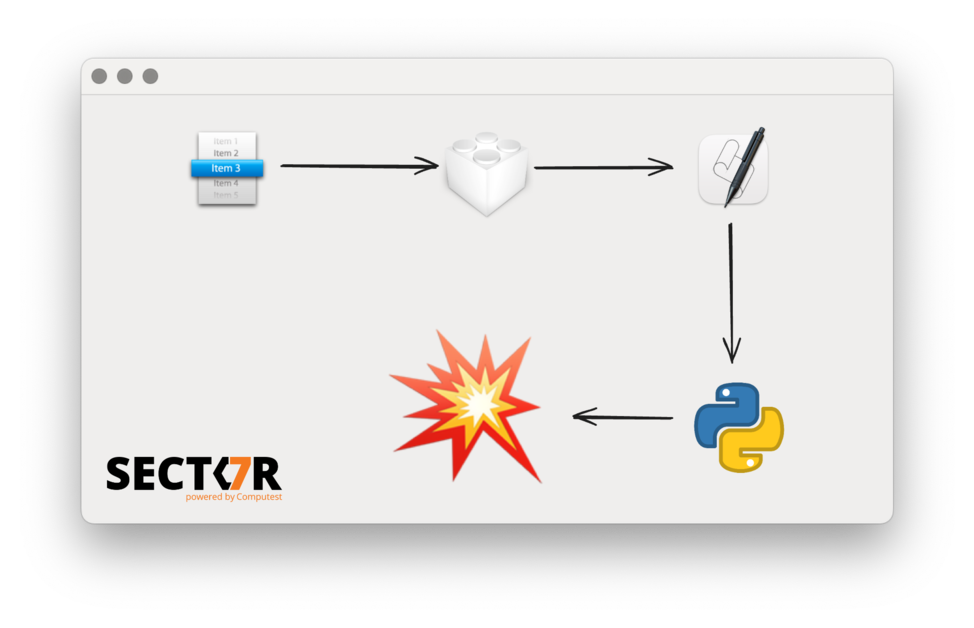
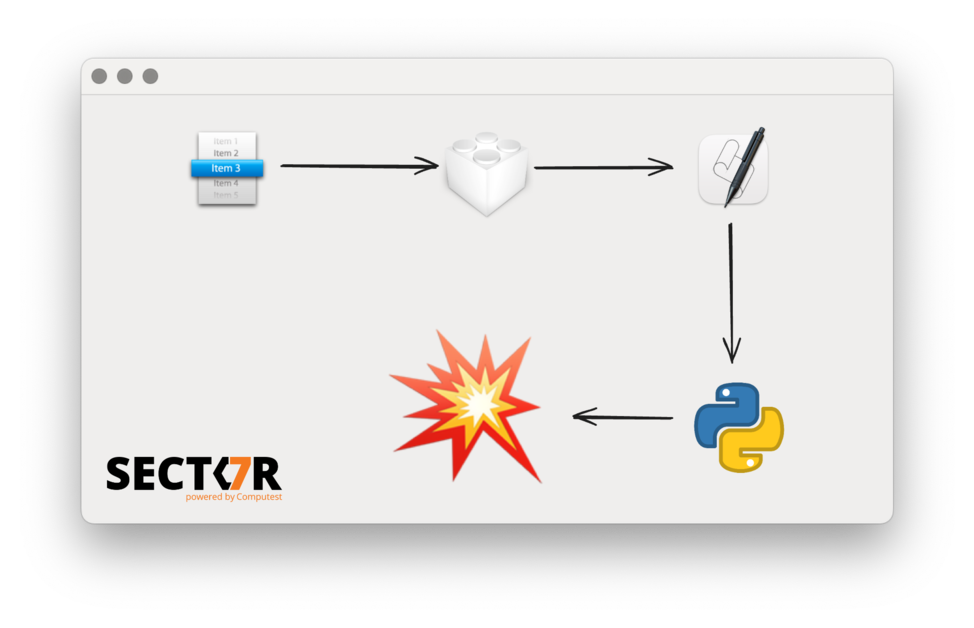
In a previous blog post we described a process injection vulnerability affecting all AppKit-based macOS applications. This research was presented at Black Hat USA 2022, DEF CON 30 and Objective by the Sea v5. This vulnerability was actually the second universal process injection vulnerability we reported to Apple, but it was fixed earlier than the first. Because it shared some parts of the exploit chain with the first one, there were a few steps we had to skip in the earlier post and the presentations.
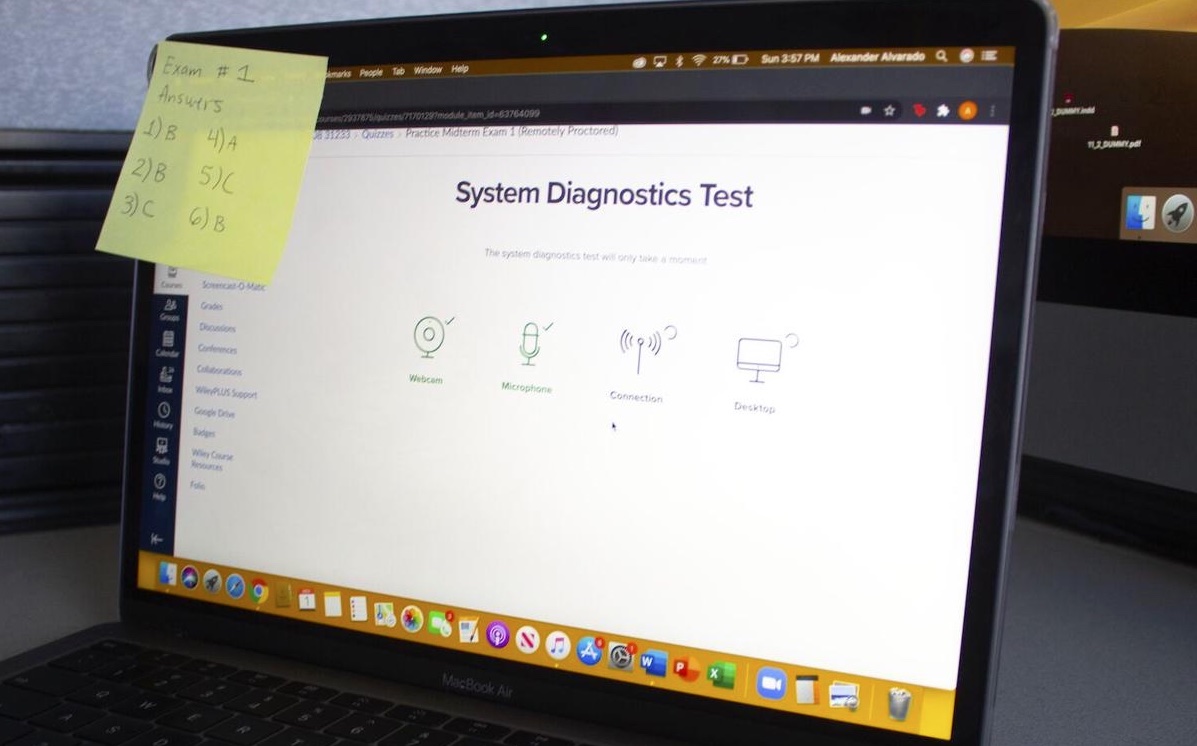
The switch to online exams In February of 2020 the first person in The Netherlands tested positive for COVID-19, which quickly led to a national lockdown. After that universities had to close for physical lectures. This meant that universities quickly had to switch to both online lectures and tests.
For universities this posed a problem: how are you going to prevent students from cheating if they take the test in a location where you have no control nor visibility?
On April 7 2021, Thijs Alkemade and Daan Keuper demonstrated a zero-click remote code execution exploit in the Zoom video client during Pwn2Own 2021. Now that related bugs have been fixed for all users (see ZDI-21-971 and ZSB-22003) we can safely detail the bugs we exploited and how we found them. In this blog post, we wanted to not only explain the bugs and our exploit, but provide a log of our entire process.
Recently, we spent some time looking at the support for IPsec VPNs in iOS. In particular, we where interested in whether a malicious VPN app could, in some way, attack the OS itself.
Last year Apple launched Sign in with Apple, which allows you to sigin in to services using your Apple ID. We identified a critical vulnerability in the service from Apple, which allowed an attacker to obtain authentication tokens which could be used to access a users iCloud account.
During a short review of the Jenkins source code, we found a vulnerability that can be used to bypass the mutual authentication when using the JNLP3 remoting protocol. In particular, this allows anyone to impersonate a client and thereby gain access to the information and functionality that should only be available to that client.
DNS rebinding attacks are a common attack technique against local applications, in order to bypass the same origin policy. The use of HTTPS has always been considered to be an effective mitigation against this attack. In this post we describe a new technique that enables the DNS rebinding attack against a HTTPS target.